The conference is hosted by the Data and Democracy Initiative at University of California at Berkeley. Do let me know if you would like your work included as part of the dialogue.
Event: Pan Optics: Perspectives on Digital Privacy & Surveillance
March 6, 2014 11am-4:30pm
Banatao Auditorium, Sutardja Dai Hall
Presented by CITRIS, CITRIS Data & Democracy Initiative, UC Davis Research Initiative in Digital Cultures
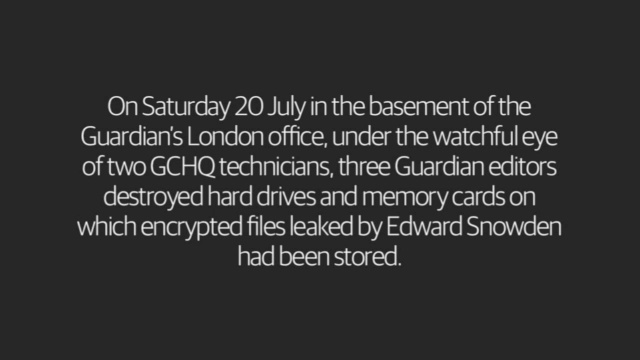
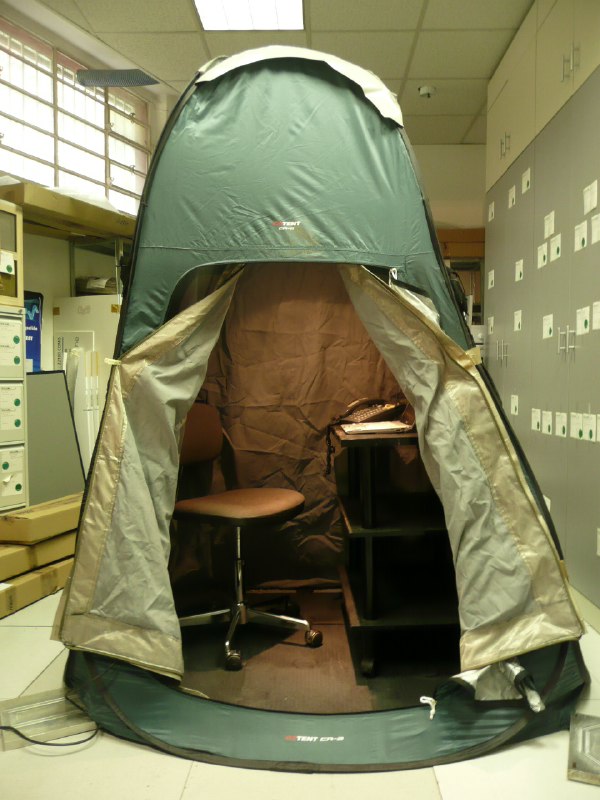
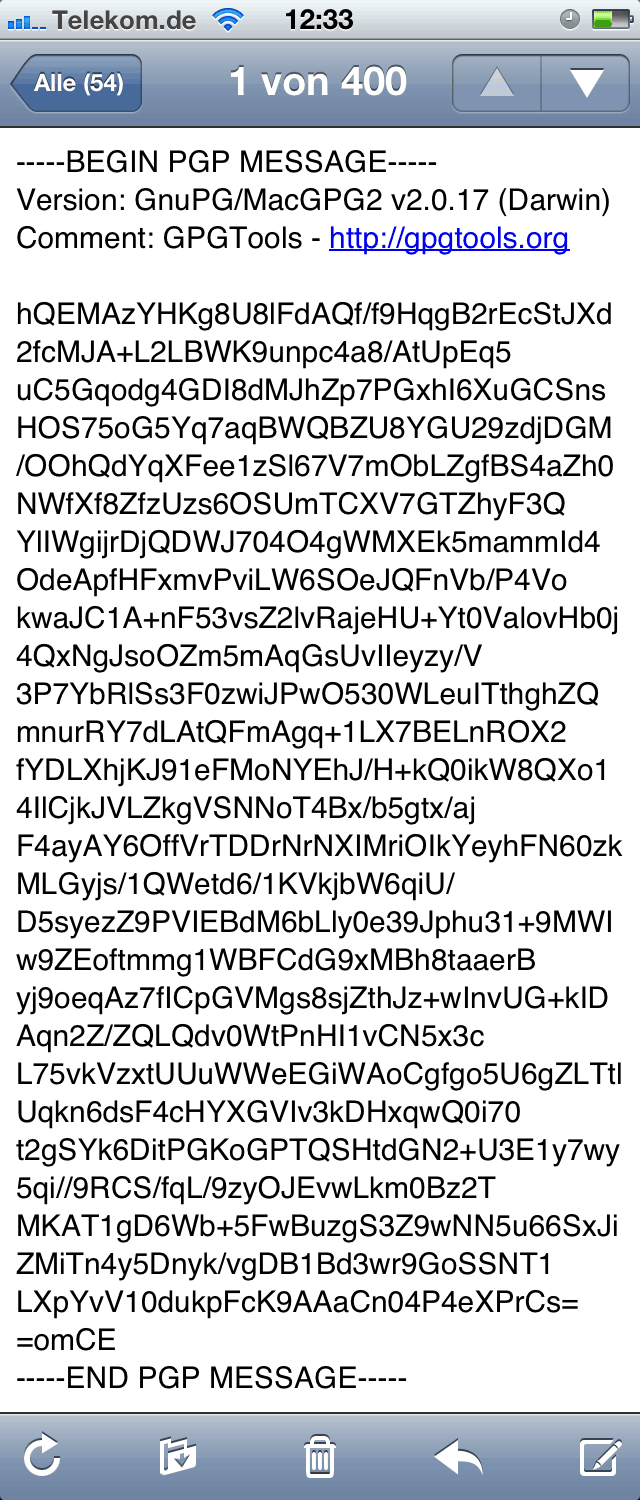
“Recent disclosures about the NSA’s international and domestic surveillance activities have stimulated overdue policy discussions among politicians and outrage among activists. The revelations have also suggested a need to address issues of privacy and surveillance on a broader level across a range of disciplines.
As a pervasive practice employed by governments, corporations, and individuals, routine data collection and ubiquitous camera technology are shifting boundaries and cultural expectations about what should and should not be shared. This symposium will bring together scholars and practitioners from a range of disciplines to discuss privacy protections, surveillance methods, and modes of resistance in a digital age.”
http://democracy.citris-uc.org/